Complete endpoint data loss prevention (DLP)
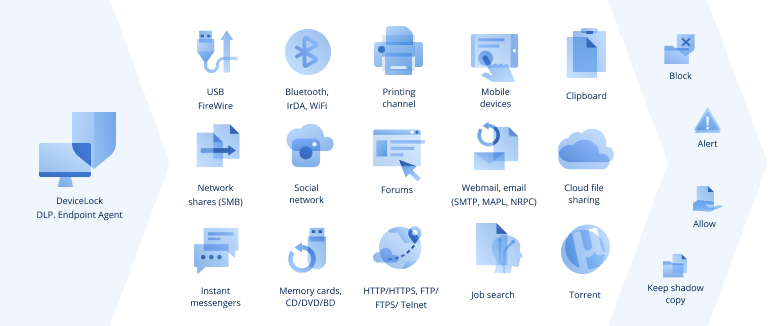
✓ Endpoint device control over data flows to peripheral devices
and ports (copy and pasting, screenshots, syncing BYODs, etc.) to prevent
internal data leaks.
✓ Control over data access and transfers through network communications
to protect against data leaks carried through the network such as
social engineering.
✓ Real-time content filtering and classification, including OCR, to ensure
no sensitive information can be leaked.
✓ Monitoring of user activity and collection of shadow and event logs
to support regulatory compliance, infosec audits or breach investigations.
✓ Protection of data at rest by locating sensitive information in documents
on endpoints and network shares, alerting admins, and providing
configurable, automatic remediation actions.
✓ Cost-optimization achieved by modular architecture allowing clients
to purchase only the functionalities they need.
and ports (copy and pasting, screenshots, syncing BYODs, etc.) to prevent
internal data leaks.
✓ Control over data access and transfers through network communications
to protect against data leaks carried through the network such as
social engineering.
✓ Real-time content filtering and classification, including OCR, to ensure
no sensitive information can be leaked.
✓ Monitoring of user activity and collection of shadow and event logs
to support regulatory compliance, infosec audits or breach investigations.
✓ Protection of data at rest by locating sensitive information in documents
on endpoints and network shares, alerting admins, and providing
configurable, automatic remediation actions.
✓ Cost-optimization achieved by modular architecture allowing clients
to purchase only the functionalities they need.
Get Acronis DeviceLock DLP
After submitting the form, you will receive an email confirmation with further information.